- Platform
- Solutions
- CTEM – Expose and Manage ThreatsContinuously identify, expose and remediate critical threats
- EASM – Attack Surface ManagementThe roadmap to reducing your attack surface
- CNAPP Validation – Cloud Attack SurfaceReduce Cloud Security Noise by Focusing on What Really Matters
- Control Subsidiary RiskManage cyber risk across all your subsidiaries
- Improve Security PostureReduce risk systematically
- Manage M&A riskEvaluate candidate’s cyber risk
- Threat Center
- Learn
- Company
Threat Exposure Radar ExplainedSolutions
IONIX Cloud Exposure ValidatorProductWE ARE IONIX
Our mission at IONIX is to give security teams unmatched focus into what truly needs fixing, reducing external exposure by addressing high-impact exploitable vulnerabilities.
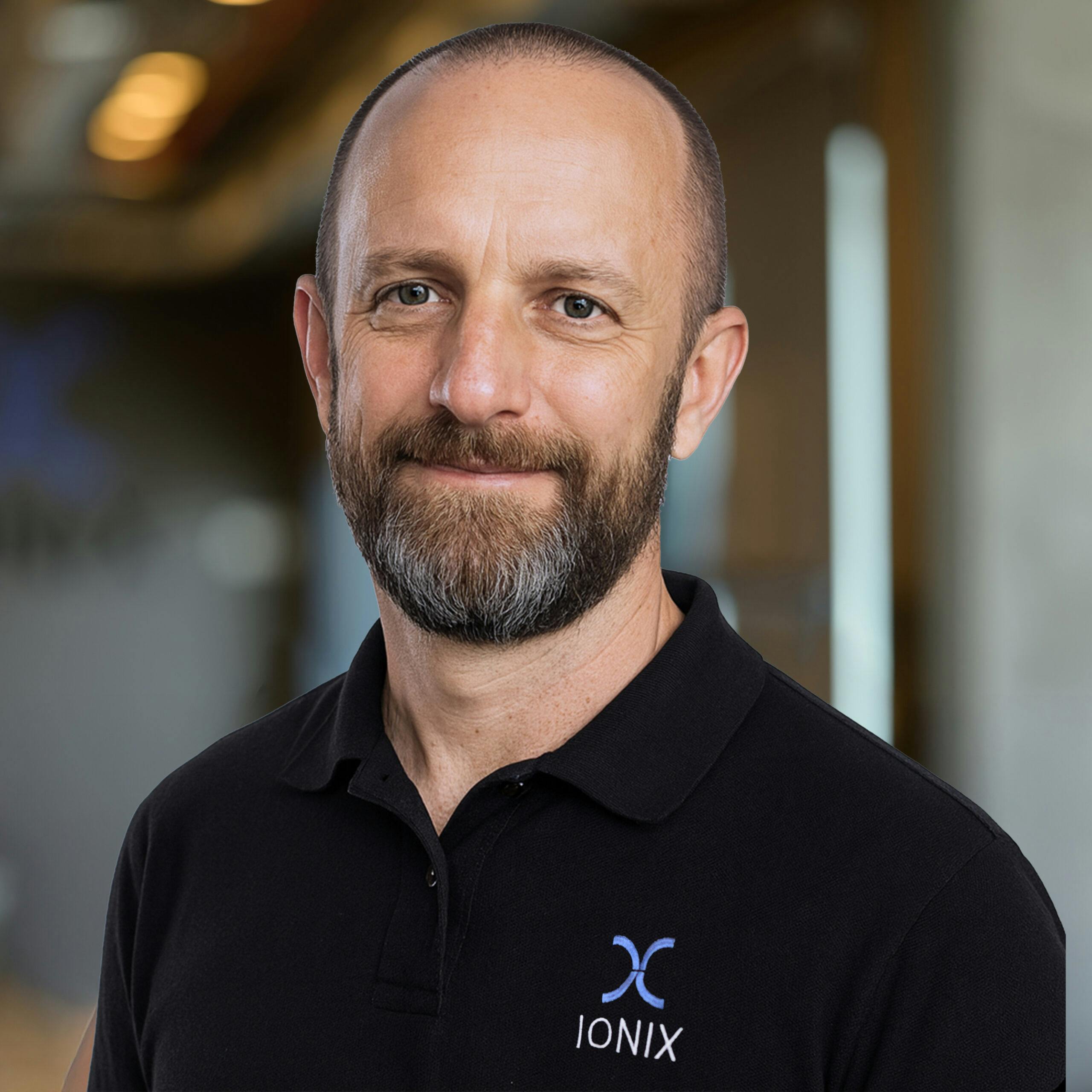
A MESSAGE FROM OUR FOUNDER
“We saw the volume and scale of cyber attacks against external enterprise assets – in governments, enterprises and SMBs. The targeted organization often had little or no awareness of the attack. We founded IONIX to do something about it.”
Dr. Nethanel GelernterCo-Founder & CTOJOIN THE IONIX TEAM
Investors
Awards & Recognition
WATCH A SHORT IONIX DEMO
See how easy it is to implement a CTEM program with IONIX. Find and fix exploits fast.
- Solutions